OFF THE WIRE
By Taylor Armerding
The security threat Stephen King warned us about.....
Remember the film "Maximum Overdrive," where machines took over and went on a murderous rampage? With cars and appliances ever more computerized, such a security threat seems a little less farfetched as we head into 2012.
Most people know that their computers and smart phones are under the constant threat of attack from hackers. But your car? Your house? Your TV and other consumer electronics?
It seems like a take on Stephen King's short story "Trucks" -- where machines come to life and go on a murderous rampage (the movie version was "Maximum Overdrive"). In this case, hackers find security flaws in the computers running our vehicles, appliances and medical devices and wreak havoc.
See the related Salted Hash blog post, "McAfee report reminds me of 'Maximum Overdrive'"
The real threat is far less dramatic, of course. But just a couple years ago, few people were seriously talking about this as a danger that might someday come to pass. As we look to 2012, however, the potential seems a lot less ridiculous, since our electronics increasingly tend to be part of a home network with an IP address -- one that can be controlled by a mobile device.
Some experts in information security believe 2012 will be a year when hackers focus more on those things.
Anup Ghosh, CEO of Invincea, says that, "in the search for more interesting devices to hack, the adversary is going to transition from traditional IT networks to embedded systems, which we normally think of as physical systems -- your car, TVs, your house, your office building. Systems that are networked and run a lot of software will be fertile ground for hackers."
Ghosh says the devices in the house simply become another node on the home network. "The devices will run an operating system kernel of some kind and accept network connections. Hackers will be able to exploit the network interface and software services running on these devices to gain privileged access to these devices. From there, they can launch attacks against other devices, store data, and exfiltrate data off the home network."
Ghosh says researchers from the University of California at San Diego and the University of Washington have already demonstrated how to hack cars through the CD player and Bluetooth interface. He says that makes any number of subsystems in the car vulnerable to exploitation. Hackers could track a vehicle, kill the ignition switch and unlock the doors.
Jason Rouse, principal security consultant at Cigital, says these capabilities are not new.
"Frankly, we've been able to break into a car for a decade," he says. "There is a worm hole attack that lets you unlock a car door just by walking past the driver. But in most cases that's not that interesting to hackers. Their primary goal is to make money."
But he does agree that there is increased danger to cars and appliances because of the convergence of controls for home or car systems with mobile devices.
Indeed, there are television ads showing mom turning the lights on and off in her house from her smart phone while she sits on an airplane waiting to leave the gate.
"You can turn on your car, you can lock or unlock it with your mobile device. That convergence comes with possible consequences," Rouse says.
"You could imagine hackers getting control of a number of vehicles and then selling that list to criminals. They can say where the vehicles are, what their license plates are, and they could unlock them all at the same time."
Rouse says the best thing consumers have going for them is that hackers tend to be lazy. "Most of them don't have the attention span to do something like that."
The primary danger, experts agree, is not to the car or the home itself but to the personal data that lies behind it -- things like passwords, credit card numbers and other information that can then be easily monetized.
When it comes to office buildings, Brenden Williams, global CTO of Marketing at RSA, The Security Division of EMC, says most companies do a good job of identifying physical assets to be secured.
For more on smart building security, see the interactive case study "Protecting Joe's Office"
"We even build security enclaves in the physical world like we might design in an electronic world. Data centers tend to be like vaults, networking closets are like locked file cabinets, and Wi-Fi is like a chain-link fence," he says.
But, he says, the systems that control the locks may not be so secure. "Are they vaulted?" he asks, "or sitting in a locked closet somewhere in an area of the network that might be accessible remotely?"
Those systems should be in a vault as well, he says.
Ghosh says the responsibility for security of home and office systems "falls squarely on the shoulders of the device manufacturers. As these manufacturers network-enable these devices, they must also engineer them for resiliency against cyber attack.
But Rouse says that may be a long time coming.
Home, auto and office systems that can be controlled remotely, "are very sexy," he says. They are sold by charm. Security is an afterthought."
Read more about network security in CSOonline's Network Security section.
skip to main |
skip to sidebar




Bill & Annie

Art Hall & Rusty


NUFF SAID.......


































































OOHRAH

ONCE A MARINE,ALWAYS A MARINE

GIVING BACK

MOUNT SOLEDAD














BIKINI BIKE WASH AT SWEETWATER










FRIENDS





BILL,WILLIE G, PHILIP










GOOD FRIENDS


hanging out

brothers


GOOD FRIENDS

Good Friends

Hanging Out





Bill & Annie
Art Hall & Rusty

Art Hall & Rusty


NUFF SAID.......
























NUFF SAID......
































Mount Soledad




BALBOA NAVAL HOSPITAL

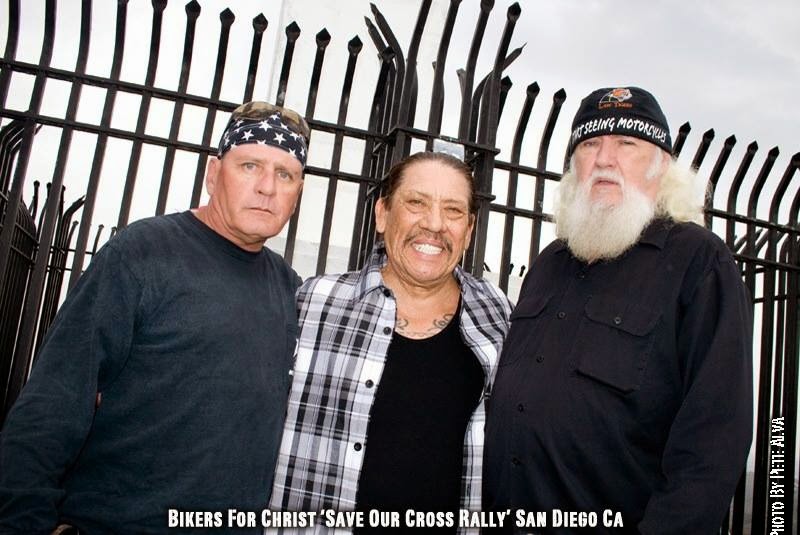
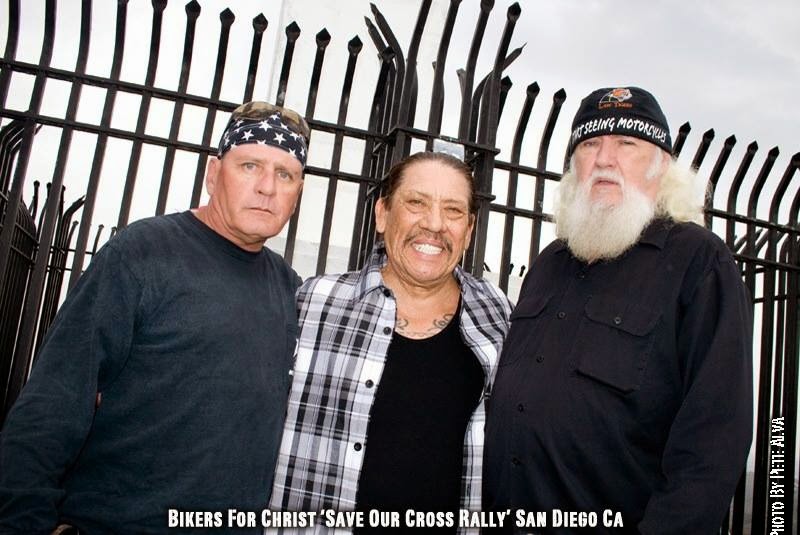
RUSTY DANNY

ANNIE KO PHILIP

PHILIP & ANNIE

OUT & ABOUT

OOHRAH...

OOHRAH
ONCE A MARINE,ALWAYS A MARINE

ONCE A MARINE,ALWAYS A MARINE
American Soldier Network GIVING BACK

GIVING BACK
CATHY & BILL

PHILIP & DANNY & BILL
MOUNT SOLEDAD
bills today

EMILIO & PHILIP

WATER & POWER

WATER & POWER







bootride2013




BIKINI BIKE WASH AT SWEETWATER









ILLUSION OPEN HOUSE

FRIENDS


GOOD FRIENDS



BILL,WILLIE G, PHILIP









GOOD FRIENDS

GOOD FRIENDS
Friends
- http://www.ehlinelaw.com/losangeles-motorcycleaccidentattorneys/
- Scotty westcoast-tbars.com
- Ashby C. Sorensen
- americansoldiernetwork.org
- blogtalkradio.com/hermis-live
- davidlabrava.com
- emiliorivera.com/
- http://kandymankustompaint.com
- http://pipelinept.com/
- http://womenmotorcyclist.com
- http://www.ehlinelaw.com
- https://ammo.com/
- SAN DIEGO CUSTOMS
- www.biggshd.com
- www.bighousecrew.net
- www.bikersinformationguide.com
- www.boltofca.org
- www.boltusa.org
- www.espinozasleather.com
- www.illusionmotorcycles.com
- www.kennedyscollateral.com
- www.kennedyscustomcycles.com
- www.listerinsurance.com
- www.sweetwaterharley.com

Hanging out

hanging out
Good Friends

brothers
GOOD FRIENDS

EMILIO & SCREWDRIVER

GOOD FRIENDS
Danny Trejo & Screwdriver

Good Friends
Navigation
Welcome to Bikers of America, Know Your Rights!
“THE BIKERS OF AMERICA, THE PHIL and BILL SHOW”,
A HARDCORE BIKER RIGHTS SHOW THAT HITS LIKE A BORED AND STROKED BIG TWIN!
ON LIVE TUESDAY'S & THURDAY'S AT 6 PM P.S.T.
9 PM E.S.T.
CATCH LIVE AND ARCHIVED SHOWS
FREE OF CHARGE AT...
BlogTalkRadio.com/BikersOfAmerica.
Two ways to listen on Tuesday & Thursday
1. Call in number - (347) 826-7753 ...
Listen live right from your phone!
2. Stream us live on your computer: http://www.blogtalkradio.com/bikersofamerica.
A HARDCORE BIKER RIGHTS SHOW THAT HITS LIKE A BORED AND STROKED BIG TWIN!
ON LIVE TUESDAY'S & THURDAY'S AT 6 PM P.S.T.
9 PM E.S.T.
CATCH LIVE AND ARCHIVED SHOWS
FREE OF CHARGE AT...
BlogTalkRadio.com/BikersOfAmerica.
Two ways to listen on Tuesday & Thursday
1. Call in number - (347) 826-7753 ...
Listen live right from your phone!
2. Stream us live on your computer: http://www.blogtalkradio.com/bikersofamerica.
Good Times

Hanging Out

Key Words
- about (3)
- contact (1)
- TENNESSEE AND THUNDER ON THE MOUNTAIN (1)
- thinking (1)
- upcoming shows (2)
Blog Archive
-
▼
2011
(5448)
-
▼
December
(390)
- The security threat Stephen King warned us about?
- DOJ Charges Seven in Massive Clickjacking Scheme
- Economist Who Predicted the 2008 Crash Gives Chill...
- Boise, ID - Boise gangs getting more violent
- AUSTRALIA - Police arrest bikie over cafe shooting
- San Jacinto Valley, CA - Crime dominated the news ...
- AUSTRALIA - Bikie associate threatened murder wit...
- NEW MEXICO - Alleged Mongols Murderers Arrested
- CA - SAN DIEGO: 'Synthetic' marijuana is problem f...
- CA - Alsops could face criminal charges
- MASSACHUSETTS - Missing drug evidence points to ‘r...
- RAGE CHOPPERS.....ISN'T THAT A BIG BEAR MODEL
- UNITED STATES COURT OF APPEALS
- CA - Fresno men arrested with guns, drugs and gear...
- Case law on federal preemption....
- US Defenders - Contact President Obama and demand ...
- CA - ESCONDIDO: Police set up checkpoint in downto...
- Canada - KELOWNA, B.C. - Mountie hurt trying to br...
- CANADA - Hells Angels associates face charges afte...
- AUSTRALIA - Man arrested over SA bikie shootout
- Laconia, NH - If you don't like Bike Week, just st...
- NEW MEXICO - Two Murder Suspects Arrested in Las C...
- CALIFORNIA - Motorcycle Cops May Lose Bike-Washing...
- CHECK OUT MIKE AND RUTH SHOW SOME SUPPORT,LOVE W...
- ILLINOIS - Mandatory Seat Belts and Motorcycles By...
- CA - VISTA: Courthouse checkpoint lands driver beh...
- CALIFORNIA - ENERGY: 2011 gas prices set record high
- CALIFORNIA - Ciccone, Kozlowski To Testify At Able...
- CANADA - The Ottawa Hells Angels president and tha...
- Your 'Human-to-Animal' Tweets Aren't Safe, Privacy...
- MASSACHUSETTS - Please review and forward to other...
- California Courts Will See a Raft of New Judges
- IF YOU SEE SOMETHING, FILM SOMETHING
- Bikers 4 Battalions at Bigg H-D
- Lewisburg, PA - Peniteniary tries to curb inmate f...
- AP Photographer Tracks Down Wounded Marine Across ...
- 'Unwavering respect' Patriot Guard Riders shield m...
- SC: Helmet Law, here we go again!
- AUSTRALIA - Police intercept suspected armed bikie
- MASSACHUSETTS - Taunton cop: 'Statistics prevail' ...
- KENTUCKY: COME AND TAKE IT....
- Support bill reducing motorcycle noise in N.H.
- Oath Keepers Launches National Effort to Recall an...
- At Year's End, DAV Has You to Thank.......
- How wealth of members of Congress has TRIPLED in 2...
- MASSACHUSETTS - Special driver's license star make...
- NCOM BIKER NEWSBYTES
- “I can do whatever I want” says badge-wearing indi...
- No title
- SOPA, the Stop Online Piracy Act...........
- Thomas Peele: California should open police person...
- Get the Hell out of Canada......
- You decide... PLEASE WATCH - WOW What a Statement
- California soldier shot at his homecoming party.....
- On the issue of helmet laws...here is someone you ...
- CALIFORNIA - ID errors put hundreds in L.A. County...
- A Soldier's Christmas!
- CALIFORNIA - Local Group Donates Bikes Christmas M...
- AUSTRALIA - Bikies back ousted Comancheros leader
- Best Marine Joke........
- Breasts to Sell Beer. Good! Breasts To Feed Baby. ...
- Challenge to California's Combined Reporting Requi...
- California to stop towing unlicensed drivers.......
- NEW HAMPSHIRE - Judge Rules Again That Towns Can’t...
- Updating The Mongols Case Again........
- It’s Not a UFO, Just a Killer Drone for an Aircraf...
- CALIFORNIA - Scrooge-like predictions for the New ...
- CA - ESCONDIDO: Mayor's anti-clapping policy criti...
- Never Can Say Good-bye: Finding Romance and Suspense
- Cop To Citizen: "If You Take My Picture Again, I'm...
- WIREDecades later, a Cold War secret is revealed.....
- CA's top judge: Death penalty no longer effective....
- Hells Angel Barred from Own Court Case in Iceland,...
- CANADA - Oakville muffling motorcycles
- Santa Plays Jingle Bells with the Colt 1911
- Did Kevin and Mona Alsop Move From Big Bear Choppe...
- GREENER GRASS.
- Lady Gaga: 'Stuck On Fuckin You' (LISTEN)..
- MILITARY: Pentagon to decide fate of Camp Pendleto...
- CALIFORNIA - MURRIETA: Deputy shot peacemaker in p...
- "California" - Legalizing Marijuana: Police Office...
- SAN MARCOS, CA - EXCLUSIVE: Deputies tow shoppers'...
- CA - POWAY: DUI checkpoint, patrols net 9 arrests,...
- Riding On Ice A Harley Panhead And A Shovel
- Senators Demand the Military Lock Up of American C...
- Phoenix inmate restraint video released
- CALIFORNIA - Legalizing Marijuana: Police Officers...
- Cops Ready for War
- 'A good cause'
- “HERMIS LIVE!” YEAR END INTERNET RADIO SHOW WEDNES...
- Stephen Lendman - Obama Approves Draconian Police ...
- Bill & I, Wish All Our Readers,A Merry Christmas &...
- New Zealand - Rebel gang leader surfaces as kids'...
- AUSTRALIA - SA cops give bikie violence top priority
- UNITED KINGDOM - Joseph Lagrue jailed for Hells An...
- Celebration of Life for John Del Santo
- OREGON - New laws for driver safety
- LoJack Corporation : LoJack for Motorcycles Helps ...
- South Carolina voter ID law blocked by Justice Dep...
- Payroll tax cut OK'd by Congress, signed by Obama
-
▼
December
(390)
Bikers of America, Know Your Rights!... Brought to you by Phil and Bill
Philip, a.k.a Screwdriver, is a proud member of Bikers of Lesser Tolerance, and the Left Coast Rep
of B.A.D (Bikers Against Discrimination) along with Bill is a biker rights activist and also a B.A.D Rep, as well, owner of Kennedy's Custom Cycles
